A new Roaring Android rooting malware has been detected with the ability to disable device security settings in an attempt to perform malicious tasks in the background at the official Play store.
What is interesting? The application was smart enough to fool Google’s security mechanism by pretending that the application itself is clean first and then temporarily relocating with a malicious copy.
The researchers found security in Kaspersky Lab, a new piece of Android rooting malware Boateng that have been distributed as games applications in the Google Play store, hidden behind the puzzle game “color block”, which has been downloaded at least 50,000 times Before removing it.
Dvmap alters the malware security settings Rating Android device to install another malicious application from a third source also injects malicious code into the system operating system libraries to get root access and remain constant.
“To circumvent the security controls in the Google Play store, use the malware creators are the very interesting way: the application is made clean the store at the end of March 2017, and Christdthonh then copy damaging for a short period of time”, According to the researchers.
“I usually download a clean version on Google Play on the same day, they did it at least 5 times between April 18 and May 15.”
Here’s how Dvmap Rooting malware works
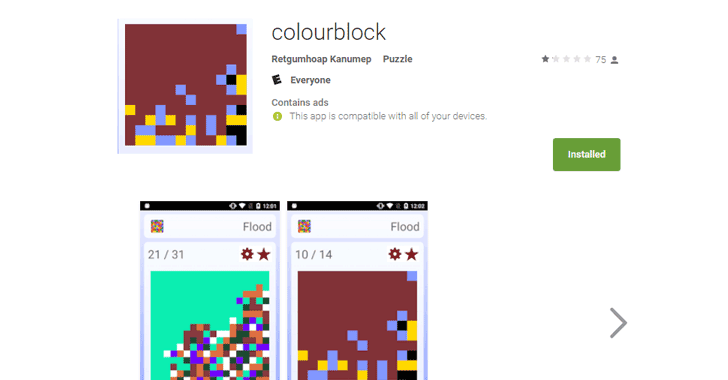
Android rooting malware application Google Play Store
Dvmap Trojan works on both the 32bit and 64bit version of Android, which once installed, and tries to get root access on the device and tries to install several drives on the system, including some written in Chinese, along with the malicious application called “Com.qualcmm.timeservices”.
To ensure that the application is harmful drive with system rights, malicious software in the system runtime libraries depending on the Android device running a version.
To complete the installation of the malicious application mentioned above, with the Trojan rights system shut down the “verification requests” function and modify the system settings to allow the application to install the application from the 3rd party application stores.
The researchers said: “On the other hand, you can grant” com.qualcmm.timeservices “application rights management application without any interaction with the user, only with the execution of the command, it is very rare that the rights of the Media Device Manager. ”
This malicious application is a third party responsible for delivering the infected device with the command and control of the attacker, giving full control of the device in the hands of the attacker server.
Also Read: How To Hack Wifi Password Through Wifiphisher?
However, according to the researchers, they did not realize the orders received by infected Android devices so far, so it is unclear “what kind of files will be executed, but may be malicious files or advertising.”
How to protect yourself from harmful software Dvmap Rooting Malware
Researchers are testing the rooting malware follows Dvmap, but at the same time, and to provide advice to users who have installed the puzzle game in question to back up their device data and restore the complete factory configuration in an attempt to mitigate malware.
To prevent you from being targeted by these applications, and always be careful about suspicious applications, even when you download from the Google Play store, and try to stick to trusted brands only. On the other hand, we always look at the comments left by other users.
Always check the permissions of the applications before installing any permissions of the application and the donation only those that have a context relevant to the purpose of the application.
Last but not least, always keep a good anti-virus application on your device that can detect this type of rooting malware and prevent it before they can infect your device and keep them up to date.



