Security researchers have discovered not one or two, but a total of seven security vulnerabilities in the popular open source Dnsmasq network software services, three of which can allow remote code execution in a vulnerable system and hijacking.
Dnsmasq network software
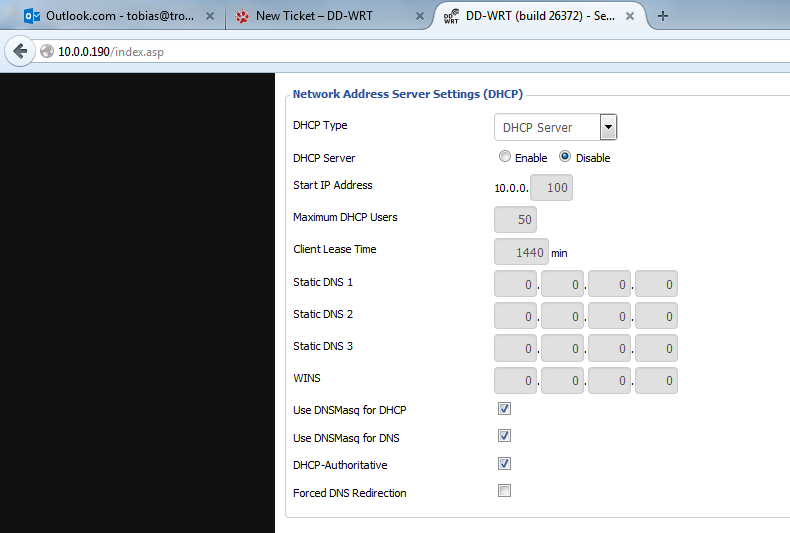
Dnsmasq network software is a lightweight network application tool widely used to provide DNS (Domain Name System), DHCP (Dynamic Host Configuration Protocol), router advertisements and network boot services for small networks.
Dnsmasq network software is pre-installed on various devices and operating systems, including Linux distributions such as Ubuntu and Debian, router, smartphones and the Internet of objects (IO). A poor search for “Dnsmasq” reveals about 1.1 million cases worldwide.
Also Read: Unofficial Anonymous Hacker Guide For Security Enthusiasts
Recently, the Google security team examined Dnsmasq network software and found seven security issues, including running remote code connected to DNS, publishing information issues and prohibition (DoS) services that can be activated through DNS or DHCP.
“We found seven different problems (listed below) in the course of our normal internal security assessments,” a Google security team wrote in a post posted on the blog on Monday.
“Once we have determined the severity of these problems, we have worked to investigate their impact and their ability to exploit and then produce an internal concept for each of them. We also work with the Dnsmasq maintainer, Simon Kelley, to produce a patch appropriate and mitigate the problem “.
Since the vulnerabilities are now made by Simon Kelley, developer and maintainer of Dnsmasq network software, Google researchers unveiled details and proof of concept (PoC) exploit code for each vulnerability.
Also Read: 16 Natural Ways to Earn Money Online
Of the seven vulnerabilities discovered by the computer, three can be exploited to execute remote code execution, three can be used in denial of service attacks and a lack of information loss.
Here is a list of all vulnerabilities:
CVE-2017-14,491 -a remote code execution vulnerability in DNS-based remote control Dnsmasq in versions prior to 2.76 is marked as the most serious that allows stack overflow, with no restrictions, affecting both the network configuration directly exposed than the internal network.
CVE-2017-14492-Another remote execution vulnerability code due to a DHCP-based stack overflow problem.
CVE-2017-14493- Another remote code execution error based on DHCP caused by a stack buffer overflow. According to Google, this defect is trivial to be exploited if used in combination with the defect (CVE-2017-14494) mentioned below.
CVE-2017-14494 A loss of DHCP information that can be combined with CVE-2017 to 14493 to allow attackers to bypass the ASLR protection mechanism and execute arbitrary code on a target system.
Also Read: Hackers Are Making $63,000 In 3 Months By Exploiting Microsoft Servers To Mine Monero
CVE-2017-14495- A defect in Dnsmasq network software that can be exploited to launch a denial of service (DoS) by depleting memory through DNS. The fault affects only Dnsmasq network software if one of these options is used: -add-mac, -add-CPE-id, or -add subnets.
CVE-2017-14496- Google’s Android operating system is specifically influenced by this DoS problem that can be exploited by a local hacker or one that is directly connected to the device. However, Google stressed that the service itself is blown, so the risk for Android users is reduced.
CVE-2017-14497- Another DoS problem where a large DNS query can block the software.
Since all issues have already been addressed with the release of Dnsmasq 2.78, users should update their Dnsmasq installations as soon as possible.
To run the device patch, be sure to update the packages on your system. Google has updated its affected services and has released security fixes to its Android partners on September 5, 2017, in the October Android security updates.
Also, assume that other relevant Google services are up to date. Kubernetes versions 1.5.8, 1.6.11, 1.7.7 and 1.8.0 have also been updated with a Dnsmasq patch.



