Recently, the whole world was filled with the computer coding errors that impact thousands WannaCry ransomware, the victim may still be encrypted after they are ready with their secret files.
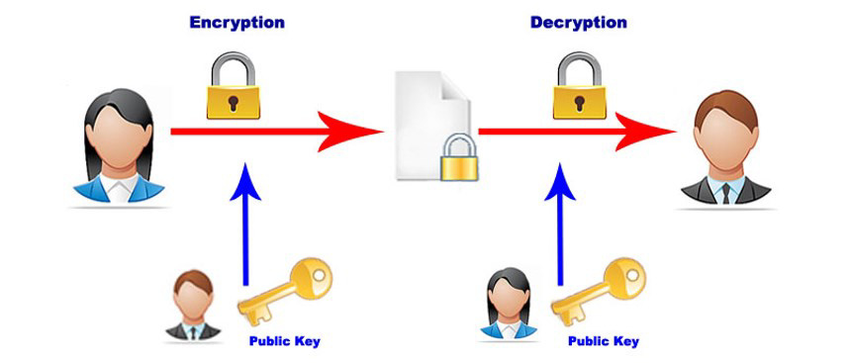
Encryption process:
The first original content file and a file read WannaCry Ransomware been encrypted “.WNCRYT” This extensive library and shops. After that, the “.WNCRYT” movement “.WNCRY” and remove the original file. According to this reason, the location and the victim may file delete characteristics change.
After encryption:
If the file is “important” folder (desktop and documents such as ransomware area code), and then deleting the original file will be overwritten before the random data. In this case, there is a chance to retrieve the file. But if the file “important” folders are located abroad, and identify the original file “% Temporary% \% d.WNCRYT” (% D numerical value is) will be moved.
These files are the original data and random data, they just drive away and is a non-system drive means software.If files that have stored using the original file reconstruction: It is possible to redirect received, with “$ Recycle” Windows Explorer folder is not overwritten the file dialog and hidden forms will be made to see this folder. After the encryption process of degradation in the list will not move the original file.
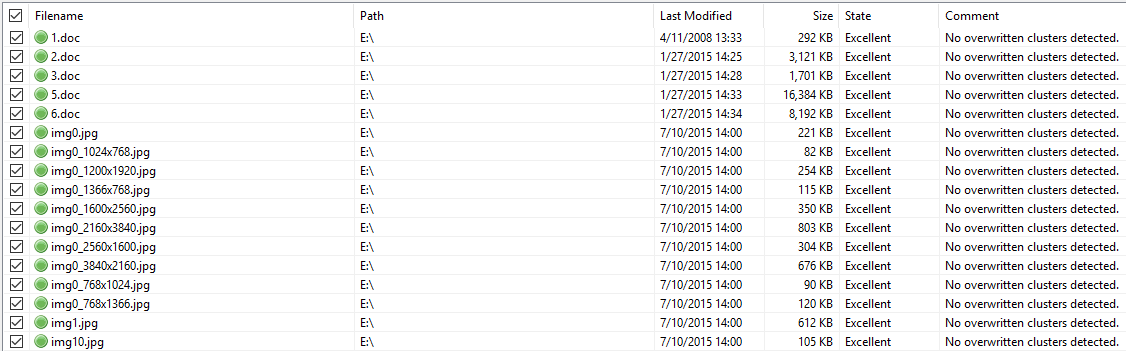
If the file is a non-system drive section is stored, redirect “$ Recycle” folder in Windows File Explorer and create a window forms secretly building this folder. After the encryption process of degradation in the list will not move the original file.
Some of the infected code mistakes, stay in the same sub-section of the original file, and not moved to “$ Recycle”. Furthermore, by safely remove the original file.
It is possible to use all the deleted file recovery software back.
Also Read: Shadow Brokers, Who Leaked WannaCry SMB Exploit, They Are Back With Zero Day Exploit
Cut Programming: A new hope for victims WannaCry Ransomware
This program offers hope to victims of code WannaCry error.
“You WannaCry efficient file, you will be able to go back to the computer has been infected by ransomware is a good chance,” Kaspersky Lab wrote in a blog post published on Thursday. “The quality of the code is very low. ”
“You are free to use the data available for installations can restore re-files. ”
Back for the first time that the file is infected by WannaCry Adrien Guinet and Benjamin Delpy, Windows XP, Windows 7, Windows Vista to work in the free WannaCry decryption device, Windows Server 2003 and Server 2008 by impossible French searchers.
It is almost a month that the disease was WannaCry world computer, but that hackers NSA ransomware EternalBlue DoublePulsar takes advantage and the exploits of Windows SMB, still has not been identified to be revealed, fit.
The verification responses to cyber police and security companies around the original WannaCry campaign continued when in the company of dark web intelligence recently revealed of Khyber criminals in China, can be based on linguistic analysis.