This time, the new version (v2) of the side channel data loss vulnerability also affects the latest Intel processors, including the latest Cascade Lake, which are otherwise resistant to attacks such as Meltdown, Foreshadow and other MDS variants (RIDL and Fallout).
Originally discovered in May of this year, ZombieLoad is one of three new types of speculative performance vulnerabilities in microarchitecture data (MDS) that affect the generation of Intel processors released since 2011.
The first variant of ZombieLoad is a Meltdown attack, aimed at the buffer filling logic, which allows attackers to steal sensitive data not only from other applications and the operating system, but also virtual machines running in the cloud with conventional equipment.
ZombieLoad v2 covers the latest Intel processors
Now, the same group of researchers has revealed details of the second variant of the vulnerability, called ZombieLoad v2 and monitored as CVE-2019-11135, found in Intel’s Intel Transactional Synchronization (TSX) extensions.
Also Read: Attackers Can Hack Sites Running On Nginx Servers By This New PHP Flaw
Intel TSX provides hardware support for transactional memory to increase CPU performance by accelerating multithreaded software and interrupting transactions when conflicting memory accesses are detected.
Intel has named ZombieLoad v2 the Transactional Synchronization Extensions (TSA) vulnerability, as it requires a local attacker to track the execution time of TSX regions to deduce memory status by comparing the execution of downtime.
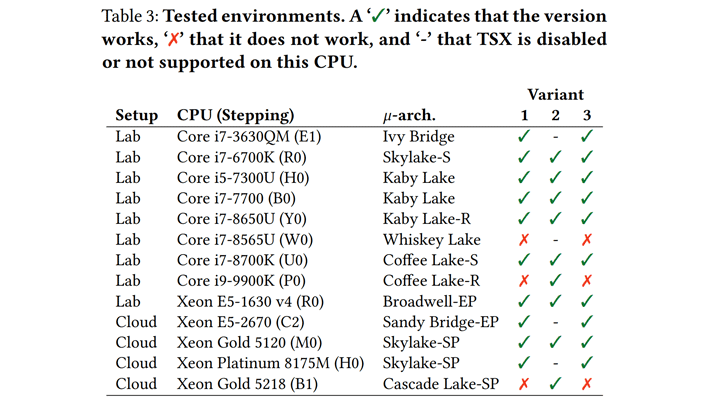
ZombieLoad v2 hits desktops, laptops and cloud computers with an Intel processor that supports TSX, including Core, Xeon, and Cascade Lake processors, the high-performance Intel processor range introduced in April 2019.
Firmware patches available for ZombieLoad v2
The researchers warned Intel about ZombieLoad Variant 2 on April 23, while they discovered and reported other MDS deficiencies that the manufacturer solved a month later in May.
Also Read: New Sim Card Flaw Let Hackers Hijack Your Phone – SimJacker
On May 10, the team also informed Intel that the ZombieLoad Variant 2 attack works against the company’s new processor lines, even though they include hardware protection against MDS attacks.
Intel has asked researchers not to disclose details of Variant 2 until the chipmaker has released a security patch with a microcode update that resolves this vulnerability.
The company has also provided MDS protections for operating system developers, virtual machine developers (VMM), software developers using Intel SGX and system administrators.
For more information on the new ZombieLoad variant, you can refer to the original research paper published by the researchers in May, which has now been updated to add information on the second variant.
Meanwhile, Red Hat has also released a script that users can use to determine if their Intel-based system is vulnerable to this vulnerability.



