Telegram Messenger zero day flaw in the version of the desktop telegram encrypted telegram end to the end application that has been exploding in nature to spread cryptomonads sap malicious software like Monero and ZCash have been discovered.
The vulnerability of Telegram was discovered by security researcher Alexey Firsh of Kaspersky Lab last October and concerns only the Windows client of the Telegram messaging software.
Also Read: A Critical Flaw Found In Grammarly Spell Checker Which Allow Hackers Steal Your Data
The blame has been actively exploited in nature since March 2017 by attackers who lured victims to download malware to their computers using their processor power to extract cryptomonads or serve as a backdoor for attackers to remotely control the machine affected, according to a blog post on Securelist.
This is how Telegram Messenger Zero Day Flaw Works
The vulnerability lies in the way the Windows Telegram client handles the Unicode RIC (U + 202E) character, which is used to code right-to-left languages such as Arabic or Hebrew.
According to Kaspersky Lab, the malware creators used an RLG Unicode hidden character in the file name that reversed the order of the characters, so that it renamed the file name and sent to the telegram users.
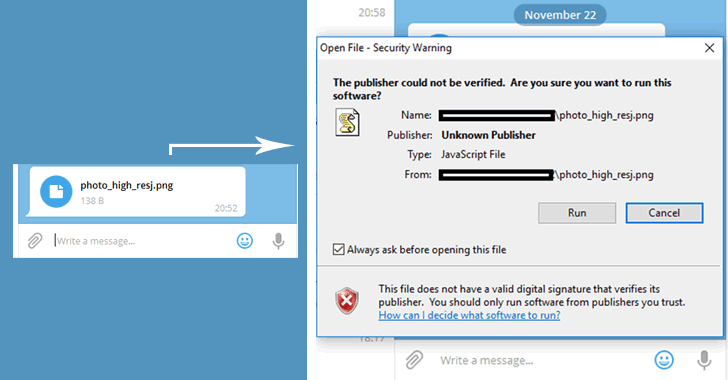
For example, when an attacker sends a file called “U + 202E photo_high_re * * gnp.js” in a message to a telegram user, the file name is displayed on the screen of the users running the last part.
Also Read: A New Undetectable Cross Rat Malware Targeting Windows, MAC OS & Linux
Therefore, the user of the telegram will see an incoming PNG image file (as shown in the image below) instead of a JavaScript file, leading to the downloading of malicious files disguised as an image.
“As a result, users downloaded hidden malware that was later installed on their computers,” says Kaspersky in his press release released today.
Kaspersky Lab reported on the vulnerability to Telegram and the company looked at the vulnerability of its products, as stated by the Russian security company: “At the time of publication, the zero-day failure has not been observed since in Messenger products ”
Hackers used Telegram to infect PC with Cryptocurrencies Miners
During the analysis, Kaspersky researchers found several day-zero exploitation scenarios in the wild by threat actors. Mainly the fault has been actively exploited for the exploration of cryptomonads of malicious software, which uses the victim’s PC computing ability to extract different types of cryptomonads, like Monero, Zcash, Fantomcoin, and others.
During the analysis of the malicious actor’s servers, the researchers also found files containing a local Telegram cache that had been stolen from the victims.
In another case, the cybercriminals successfully exploited the vulnerability to install a backdoor Trojan that used the Telegram API as a command and control protocol, allowing hackers to remotely access the computer from the back door. victim.
“After the installation, it started working in silent mode, which allowed the actor of the threat to go unnoticed on the network and execute various commands, including the additional installation of spyware”.
Also Read: 7 EFFECTIVE REASONS TO TAKE ACTION ON YOUR BOLD BUSINESS IDEA
Firsh believes that the telegram messenger zero day flaw has been exploited only by Russian cybercriminals, as “all the detected exploitation cases [researchers] that happened in Russia” and many objects have pointed out the Russian cybercriminals.
The best way to protect yourself from such attacks is not to download or open files from unknown or unreliable sources.
The security firm also recommended that users avoid sharing confidential personal information from email applications and ensure that they have a reliable enterprise antivirus installed on their systems a good software.



