If you think you’ve downloaded Sonicspy Spyware from the Google Play Store and you’re safe, then look!
Someone managed to flood third-party app store and Google Play store with over a thousand malicious applications that can monitor almost everything a user does on their mobile device to record silent calls to make outgoing calls without user interaction.
Nicknamed Sonicspy Spyware, spy software has been aggressively spread across all Android app stores, at least, February and is distributed by pretending to be a messaging and actually offers a messaging service.
Sonicspy Spyware can perform a lot of malicious activities
At the same time, Sonicspy Spyware spy applications perform various malicious activities, including mute calls and audio from the microphone to hijack the device’s camera and take pictures, make outgoing calls without the user’s permission, and send text messages to selected numbers By the attacker.
Apart from that, SonicSpy spyware also steals user information, including call logs, contacts, and Wi-Fi access information that connect to the infected device that can be easily used to control the user’s position.
Also Read: Wanna Cry Ransomware Hackers Withdraw $143,000 Through Bitcoins
Sonicspy Spyware was discovered by security researchers on the Lookout mobile security appliance. The researchers also uncovered three versions of infected messages in sonic spy’s official Google Play store, which had been downloaded thousands of times.
Although the applications in question – Sonia, Hulk and Troy Chat Messenger – have been removed from the Google Play Store, they are still widely available in third party application stores and other infected Sonicspy Spyware applications.
Connection to Iraq SonicSpy Spyware
Investigators believe the malware is connected to an Iraq-based developer and said the worldwide Sonicspy Spyware family supports 73 different remote instructions that its attacker could run on an infected Android device.
The Iraqi connection for Sonicspy Spyware comes from the similarities between Sonicspy Spyware and Spynote, another malware for Android was discovered in July 2016, which was disguised as a Netflix application and was believed to have been written by Iraqi hackers.
“For example, the two families share code similarities, regularly use dynamic DNS services running on non-standard 2222 ports,” says Services. “There are many indications that the same actor is behind the development of both. Security research looks out to bring the technology of Michael Flossman.
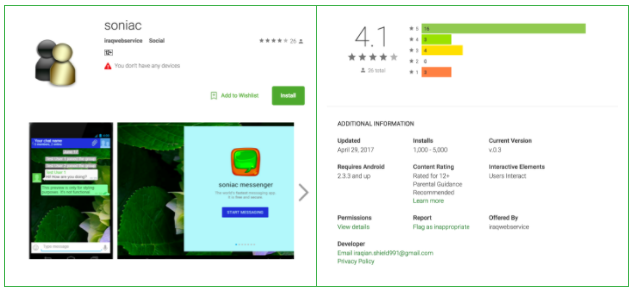
In addition, the important indicator is the name for the developer behind SoniaC, Google Play appears in the file, “iraqiwebservice”.
This is how Sonicspy Spyware works
One of the infected Sonicspy Spyware messaging applications that made it through the Google Play Store has been disguised as a communication tool called soniaC.Once installed, Sony removes the icon to start the smartphone menu to hide.
Also Read: Banking Trojan Inspired By Wannacry To Add Self Spreading Ability
Once installed, Sony removes the icon to start the smartphone menu to hide from the victim and connects to a command and control server (C & C) in an attempt to install a modified version of the telegram.
However, the application includes many features that allow malicious attackers to get almost complete control of the infected and turn it into a pocket spy that could record audio silence, make calls, take photos and steal your personal information, Logs, contacts, and details about Wi-Fi access points.
Before being removed from Google, the application had already been downloaded between 1,000 and 5,000 times, but because it was part of a family of 1,000 variants, the malware may have infected many thousands more.
Sonicspy Spyware could resume playback
Although infected applications of Sonicspy Spyware were removed from the Play Store, researchers warned that malware could re-enter the Play Store with another account for development and application interface.
“The players in this family have proven to be able to get their Sonicspy Spyware in the official application store and while it is active in the development stage and the creation process is automated, it is very likely that Sonicspy Spyware will recover in the future,” He warned.
While Google has taken many security measures to prevent malicious applications from making Google’s security controls, malicious applications continue to enter the Play Store.
Also Read: Apple Remove VPN Apps From China App Store
Just last month, we warned of malicious smart software, called Javier, that was discovered in more than 800 different Android applications that have been downloaded millions of times from the Google Play Store and have silenced sensitive user data and can perform dangerous tasks.
In April BankBot reported bank banking problem very close to the Google Play Store with the ability to gain administrator privileges on infected devices and perform a variety of malicious activities, including access to the bank rubazione victim.
In the same month, about 2 million Android users have been victims of FalseGuide malware hidden in more than 40 applications for the most popular mobile games, such as Pokémon Go Mobile and FIFA, the official Google Play Store service.
How to protect yourself from this type of malware
The easiest way to prevent it from being implemented by this type of smart malware, always careful of suspicious applications, even when downloaded from the official Google Play Store and try to rely only on trusted brands.
In addition, you always see the patches left by users who have downloaded the application and check permissions of the application before installing any application, even in official application stores and allow those permissions relevant to the purpose of the application.
Also Read: CowerSnail Is Windows Backdoor From Creators Of Sambacry Linux Malware
Also, do not download applications from third-party sources. Although in this case, the application is also distributed through the official Play Store, often victims have been infected by malware through these third-party application stores that are not trusted.
Finally, it is advisable to always keep good antivirus software on the device can detect and block malware before infecting the device and maintaining the device and applications.



