Previously, computer security researchers said details about self replicating malware security breaches this month with Official Hacker, which affects all versions of Microsoft Office, allowing hackers to create and distribute malware self-replication by macros.
Macro-based self replicating malware that essentially allows you to write more macro is nothing new among hackers, but to avoid such threats Microsoft has implemented a security mechanism in MS Office, which limits this feature by default.
Lino Antonio Bon (Lino Antonio Buono), the Italian security researcher who works in the cyber, reports on a simple technique (described in detail below), which would allow anyone to bypass the Microsoft security controls installed, and to create car-replicating malware, hidden behind an innocent Word MS documents.
Also Read: Terdot Banking Trojan Has Ability To Hack Facebook,Gmail And Twitter Accounts
What is worse? Microsoft has refused to consider this issue as a security breach in search management in the month of October this year, saying it is a feature designed to work just like MS Office DDE, which is being actively used by pirates.
A new utility “QKG ransomware”, using the same technique of self replicating malware
Interestingly, one of these malicious programs is coming. I know it was fast even before public disclosure.
Just yesterday, Trend Micro released a report on the new part of Macro-Replication-Based Self Replicating malware, nicknamed “QKG,” which uses the same MS Office feature that describes our team well.
The Trend Micro researchers have discovered QKG ransomware samples at VirusTotal, downloaded by someone from Vietnam, and I was told, rather than malware that is being actively used that it means foreclosures seem “rather a pilot project or evidence concept (PoC) in nature “.
The QKG ransomware utility uses VBA auto-closing macros, a method that allows for the execution of a malicious macro when the victim close the document.
Also Read: 16 Natural Ways to Earn Money Online – Be Like Billionaire
The latest version of QKG ransomware now includes a Bitcoin address with a small buy-back, which requires $ 300 for BTC, as shown.
It should be noted that the above Bitcoin address has not received any payment that seems to imply that the software has not yet been used to direct people.
In addition, this ransomware currently uses the same password that is difficult: “I QKG PTM17 @ @ TNA MHT-TT2! “, Which unblocks the concerned files.
Here’s how this new attack technique works
What we understand all the attack techniques, Buono shared a video with The Hacker News, which shows how an MS Word document with malicious VBA code can be used to provide a malware platform capable of replicating itself.
If you do not know how to allow, Microsoft is disabled by default external (or unreliable) macro and limited access software to model default objects in the VBA Office project, but also allows users to manually access “Trust to the VBA Objects template project “if necessary.
Microsoft Office-Macro Self Replicating Malware
With the “Trust Project Model VBA Object” trust MS Office all macros and automatically execute a code, without security warnings or require the consent of the user.
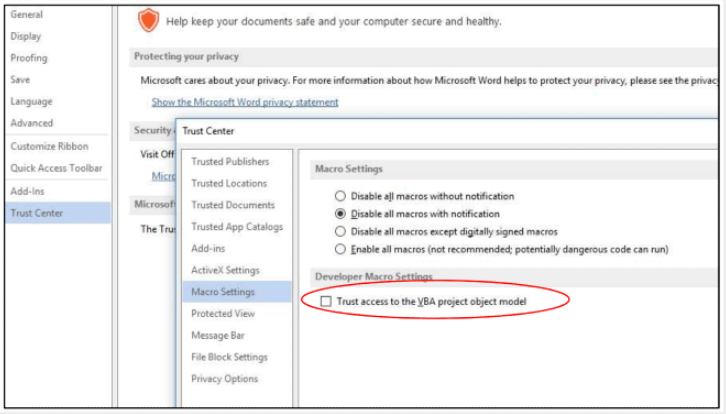
Okay, he found that this option can be enabled/disabled simply by modifying the Windows registry, which causes macros can write the macro without the consent and knowledge of the user.
Also Read: Critical Tor Browser Vulnerability Leaks User’s Real IP Address
As you can see from the video, the malicious file MS Doc, created by Buono, does the same: first, it modifies the Windows registry, and then enters the same payload macro (VBA code) into each document file that the victim creates, edits or opens. only on his system.
Victims will unconsciously be responsible for the spread of malicious software
In other words, if the victim erroneously allows the malicious doc file to run macros once, its system remains open for macro-based attacks.
In addition, the victim will also unconsciously be responsible for distributing the same malicious code to other users by sharing infected Office files from their system.
This method of attack can be more alarming if you get a file of a malicious document from a trusted contact that has already been infected with this malicious software, turning it into an attack vector for others.
Although this method is not used in nature, the researcher believes that it can be used to spread dangerous self replicating malware programs that can be difficult to process and complete.
Also Read: ‘LeakTheAnalyst’ Arrested: Hacker Who Claimed To Have Hacked FireEye
Because this is a legitimate function, most anti-virus solutions do not prevent or block Microsoft Office documents with VBA, or the technology company plans to issue a fix that limits this feature.
Good suggestion “To mitigate (partially) the vulnerability, you can move the AccessVBOM registry key from HKCU HKCU to HKLM, making it available only to the system administrator.
The best way to protect yourself from malware is to be careful with unsolicited e-mail messages and never click links within those documents unless you properly check the source.



