Security researchers are warning of ropemaker exploit, a new easy-to-use email makeup that could allow an attacker to transform an apparently benign email into failure after it has already been sent to their email.
Nicknamed Ropemaker exploit (means handling post-partum remote electronic attacks, keeping email risks), the trick was discovered by Francisco Ribeiro, a researcher at e-mail security firm Mimecast.
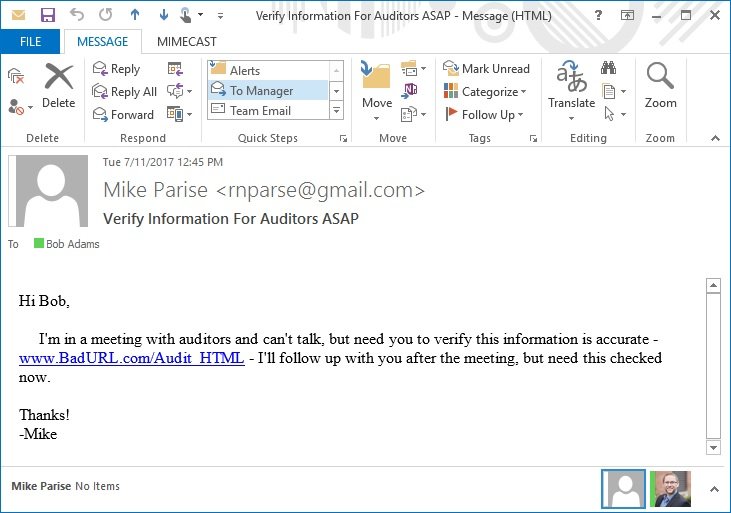
A Ropemaker exploit effective exploiting the attack could allow an attacker to modify the content of an email sent by the user in remote mode itself, for example by swapping a URL with the malicious user.
Also Read: Smart Devices Can Be Hacked By CovertBand Attack To Track Activities
This can be done even after the email has already been delivered to the recipient, and they have done so through all the necessary filters to protect spam and security, without requiring direct access to the computer or application Of the recipient’s email, exposing hundreds of millions of users of desktop mail clients to malicious attacks.
Ropemaker exploit CSS (Cascading Style Sheets Style) and Hypertext Markup Language (HTML) abuses that form a fundamental part of the way information is presented on the Internet.
“The origin of Ropemaker exploit lies at the intersection of email and Web technologies, specifically CSS (Cascading Style Sheets) style used with HTML,” writes Merycast Senior Product Marketing Administrator Matthew Gardiner in a blog.
“While using these web technologies made e-mail more visually appealing and dynamic than its purely text-based predecessor, it also introduced a vector of exploitable attack for e-mail.”
Since the CSS is stored remotely, the researchers claim that a malicious user can edit the contents of an email via changes started do remotely for the “style” of the desired email is retrieved remotely and Presented in ‘User without the recipient, knowing this.
According to the researchers, the Ropemaker attack could be exploited depending on the creativity of the threat actors.
Also Read: Android Banking Trojan Targeting Non-Banking Apps That Require Card Payments
For example, attackers could replace a URL that originally targeted the user to a legitimate site with a malicious user who sends the user to a compromised site designed to infect users with malware or steal confidential information such as credentials and details banking.
While some systems are designed to detect the URL switch by preventing users from opening the malicious link, other users may be left at risk for security.
Another attack scenario, called “Exploit Matrix” by the Mimecast, is more sophisticated than the “Exploit Switch”, and therefore much more difficult to detect and defend.
In an Exploit Matrix attack, attackers write an array of text in an email and then use the remote CSS to selectively control what is displayed, allowing the attacker to show what they want, including adding malicious URLs In the body of the email.
Also Read: More A Than A 1000 Sonicspy Spyware Found On Google Play Store
This attack is more difficult to defend because the initial email address received by the user does not display any URLs, but most software systems do not mark the message as harmful.
“Because the URL is made after delivery, an email gateway solution like Mimecast can not find, edit, or control the target site in one click, because at the time of delivery there would be no URL to detect”, Reads The report. “For this, it would be necessary to interpret CSS files, which is beyond the scope of existing e-mail security systems.”
Although the security company did not detect the Ropemaker attack in the wild, it is believed that this does not mean that the attack “is not used somewhere outside the Mimecast” point of view.
According to the security company, Ropemaker exploit could be used by hackers to bypass cheating security systems and even the most common experienced users in technology in interaction with a malicious URL.
To protect against this type of attack, users are advised to rely on Web-based email clients such as Gmail, cloud, and Outlook, which is not affected by CSS exploit in Ropemaker exploit style, according to Mimecast.
However, email clients such as desktop and mobile versions of Apple Mail, Microsoft Outlook, and Mozilla Thunderbird are vulnerable to Ropemaker attacks.



