North Korea’s personal homegrown PC operating device Redstar, it’s presupposed to be completely hacker-proof and extra comfortable than the foreign OS, like Microsoft’s home windows, can effortlessly be hacked remotely.
A set of hackers managed to break into pink celebrity OS — North Korea’s government-sanctioned Linux-primarily based OS — the usage of only a hyperlink.
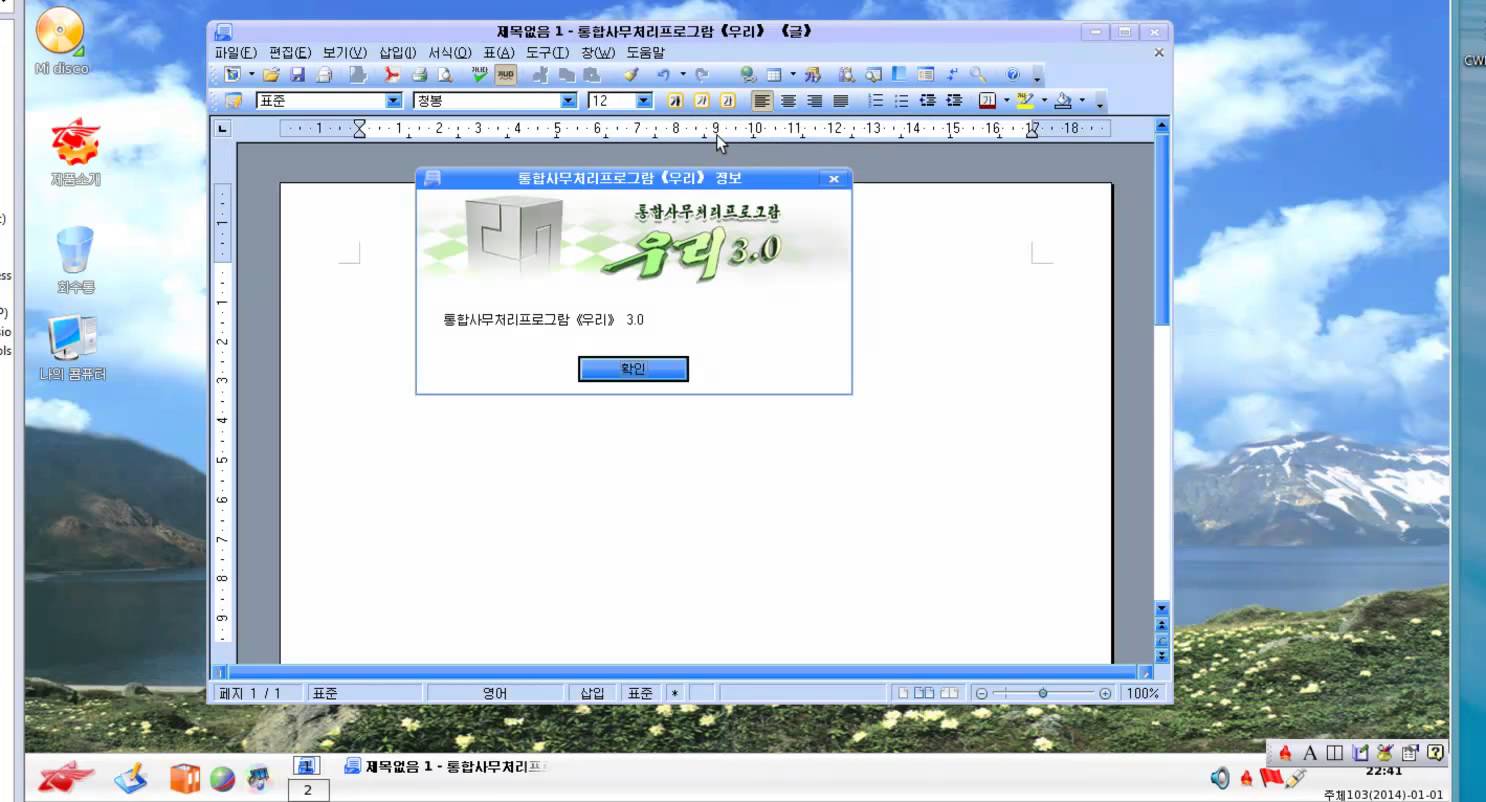
Red celebrity OS is North Korea’s homegrown OS that looks remarkably much like Apple’s OS X and offers North Korean authorities extra control over the computers, imparting not handiest security however also spying equipment that assist track files in a manner that if the government needs, every little bit of consumer’s records can be traced without problems.
In keeping with the facts safety enterprise Hacker house, pink famous person OS carries an important vulnerability that makes it possible for hackers to benefit remote get right of entry to any PC jogging North Korea’s OS simply by way of tricking victims into starting a link.
The contemporary model of crimson superstar OS ships with a Firefox-based web browser called Naenara, and in step with researchers, the “trivial remote take advantage of attack vectors” contained in the web browser allows attackers to hack into the gadget.
Right here’s how they make the most work:
The Hacker residence hackers exploited a specific red megastar application that handles Uniform Request Identifiers (URI) – a string of characters used to identify resources in a network.
Hackers noted that the “mailto” URI request used for e-mail will be exploited by using hackers to remotely “execute arbitrary instructions.”
since this unique URI does not take away requests from the software’s command line, hackers should “trivially achieve code execution” simply with the aid of injecting malicious links into the command line.
“whilst probing for vulnerabilities it changed into noticed that registered URL handlers had been exceeded to a command-line software ‘/usr/bin/nnrurlshow.’ This utility (apart from having null ptr de-refs and other cute insects) takes URI arguments for registered URI handlers whilst coping with application requests consisting of ‘mailto’ and ‘cal,’ the Hacker house hackers explains.
“Naenara would not sanitize the command line while managing these URI argument requests and as such, you can trivially gain code execution using passing malformed hyperlinks to the nnrurlshow binary.”
In brief, this protection flaw can be used effortlessly to install malware or exploit PCs strolling the purple megastar operating the machine.
Rival South Korea has long blamed North Korea for mounting diverse cyber attacks against its authorities, army, and different businesses.
just recently, the South Korean military blamed North Korea for breaching its army cyber command. A spokesman for the army cyber command told BBC that classified information became thought to be stolen, even though it’s not clear exactly what facts were accessed.




Going to put this arclite to good use now.