After discovering the massive botnet VPNFilter malware, security researchers have discovered another huge botnet ( Prowli Malware )that has already touched more than 40,000 servers, modems, and Internet-connected devices belonging to a large number of organizations around the world.
Prowli’s double operation, the campaign has spread malicious programs and injected malicious code to detect the server and websites around the world using various attack techniques, including the use of exploits, forcing the words of pass and abuse of vulnerable configurations.
Discovered by researchers from the GuardiCore security team, Operation Prowli malware has already affected more than 40,000 victim machines for more than 9,000 companies in various sectors, including finance, education, and government agencies.
Also Read: Two New Malware Linked To Hidden Cobra Hackers- FBI Issues Alert
Here is the list of devices and services infected by the Prowli malware:
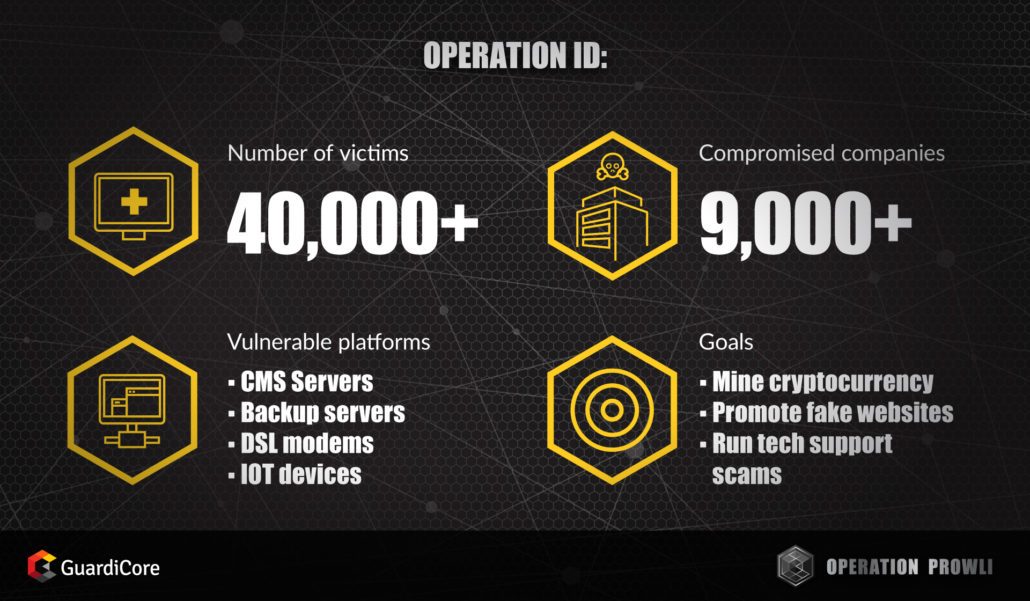
- Drupal and WordPress CMS Servers Hosting Popular Websites
- Joomla! servers running the K2 extension
- Backup servers running the HP Data Protector software
- DSL modem
- Server with an open SSH port
- PhpMyAdmin installations
- NFS boxes
- Server with exposed SMB port
- Vulnerable Internet-of-the-Things (IoT) devices
- All the above goals were infected using a known vulnerability or hypothesis of powers.
- The Prowli malware injects the cryptocurrency miner
Since attackers behind the Prowli malware attack mistreat infected devices and websites to extract or run a crypto-currency script that redirects them to malicious websites, researchers believe they are more focused on money rather than ideology or espionage.
According to GuardiCore researchers, compromises devices have been found infected by a minor Monero cryptocurrency (XRM) and the malware worm “R2R2” written in golang that performs brute-force SSH attacks from infected devices, which allows Prowli malware to support new devices.
In simple words, “R2R2 randomly generates blocks of IP addresses and access attempts repeatedly iteratively performing SSH abruptly with a user dictionary and password. Once you stop, make a series of commands on the victim, “explain the researchers.
These commands are responsible for downloading multiple copies of the worm for different CPU architectures, a cryptocurrency miner, and a configuration file from a remote hard-coded server.
Malicious users also encourage users to install malicious extensions
In addition to minor cryptocurrency, hackers also use a well-known open-source web shell called “WSO Web Shell” to change compromised servers, allowing an attacker to redirect visitors to fake sites that distribute websites. Malicious browser extensions.
The GuardiCore team traced the campaign across different networks around the world and found the Prowli malware campaign associated with different sectors.
“Over a period of three weeks, we have captured dozens of these daily attacks of more than 180 IPs from various countries and organizations,” the researchers said. “These attacks led us to investigate the infrastructure of the attackers and to discover a vast operation that attacks several services.”
Protect your devices from Prowli malware attacks
Because attackers use a combination of known vulnerabilities and removal of credentials for compromised devices, users must ensure that their systems are current and up-to-date and always use passwords for their devices.
In addition, users should consider locking down systems and segmenting vulnerable or hard-to-protect systems to separate them from the rest of their network.
At the end of last month, he was found a massive botnet, dubbed VPNFilter, which infected half a million routers and storage devices from a wide range of manufacturers in 54 countries with a malware that has the capacity to conduct computer operations of destruction, surveillance and Man- attacks in the middle.



