Cybersecurity researchers have discovered a new mobile surveillance malware program developed by a Russian defense contractor and sanctioned for interfering in the 2016 US presidential election.
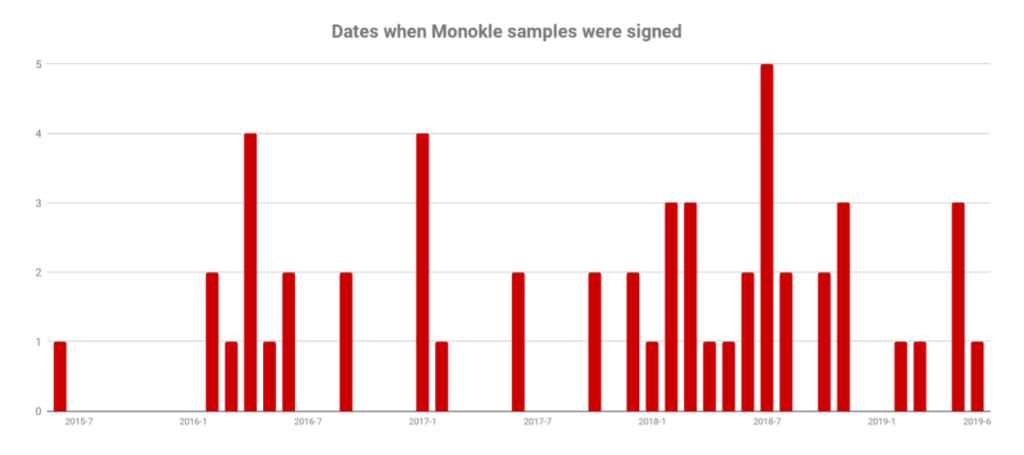
The duplicate Monokle surveillance malware, a mobile trojan with remote access, has actively targeted Android phones, at least since March 2016, and is mainly used for targeted attacks against a limited number of people.
According to the Lookout security researchers, Monokle surveillance malware has a wide range of spyware features and uses advanced data exfiltration methods, even without requiring root access to the target device.
How bad is the Monokle surveillance malware to monitor
In particular, the malware uses Android accessibility services to remove data from a large number of popular third-party applications, including Google Docs, Facebook Messenger, Whatsapp, WeChat and Snapchat, reading the text displayed on the device’s screen at any moment.
Also Read: New EvilGnome Backdoor Implant Spies On Linux Users
The malware also retrieves the user’s predictive text dictionaries to “understand the topics of interest to the target” and also attempts to register the phone screen during a screen unlock event to compromise the phone’s PIN, sequence or password.
Furthermore, if root access is available, the spyware installs the specified root CA certificates specified by the attacker in the list of trusted certificates on the compromised device, which allows attackers to easily intercept SSL-encrypted network traffic through the human network. Medium attacks (MiTM).
Other Monokle surveillance malware features include:
- Tracking of the device position
- Record audio and calls
- Get the items on the screen
- Keylogger and device fingerprinting
- Get a view and call the history
- Take photos, videos, and screens
- Receive e-mails, text messages and messages
- Steal contacts and calendar information
- calls and text messages on behalf of the victims
- Run arbitrary shell commands as root if you log in to the root
In total, Monokle surveillance malware contains 78 different predefined commands that the attackers can send via SMS, telephone calls, e-mail exchange via POP3 and SMTP, as well as incoming/outgoing TCP connections, indicating to the malicious software to filter the requested data and send it to a remote team of attackers. -and management server.
Spyware disguised as PornHub and Google’s Android apps
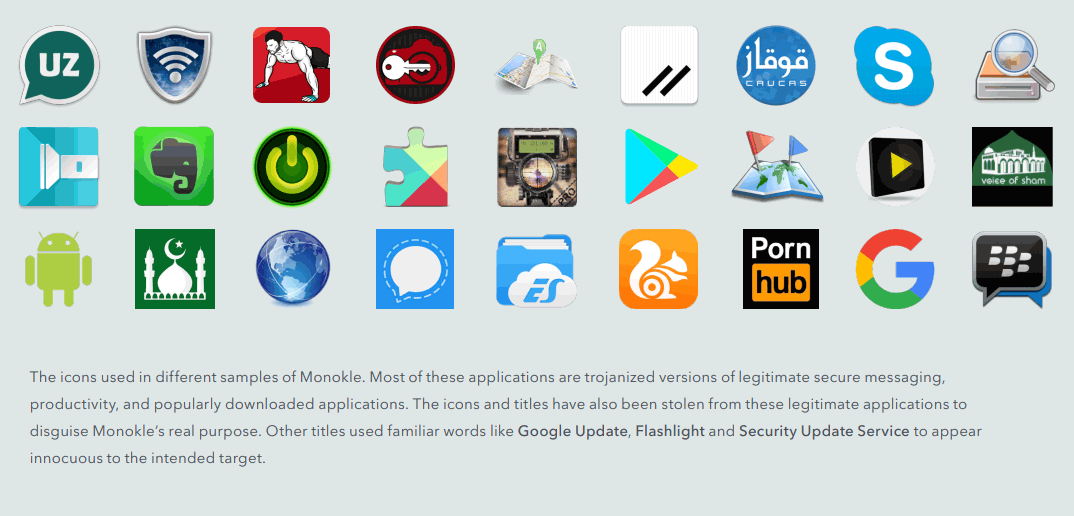
According to the researchers, the attackers distribute Monokle through fake applications like Evernote, Google Play, Pornhub, Signal, UC Browser, Skype and other popular Android apps.
Most of these applications also include legal functionality, preventing target users from suspecting that applications are harmful.
Furthermore, some recent Monokle samples are even bundled with Xposed modules that allow the malware to modify some of the system’s functions, ultimately expanding its ability to intercept and hide its presence in the process list.
Also Read: New Instagram Login Vulnerability Allow Hackers To Takeover Your Account In Minutes
The malware package uses the DEX file in its resource folder, which “includes all the cryptographic functions implemented in the open-source spongycastle library, various e-mail protocols, extraction and exfiltration of all data, serialization, and deserialization of data using the Thrift protocol and the rutting and interception functionality, among others.”
The new malware for Android and its features remind us of the powerful Pegasus malware, developed by the Israeli group NSO for Apple iOS and Google Android devices.
However, unlike the Russian monokle surveillance malware, Pegasus has powerful zero-day exploits that install spyware on the target device, almost without interacting with the user.
Pegasus had previously been used to attack human rights defenders and journalists, from Mexico to the United Arab Emirates, and again last year against an Amnesty International employee in Saudi Arabia.
Russian Defense Contractor STC Developed Monokle surveillance Malware
Monokle surveillance malware was developed by the Russian company Special Center Ltd. (STC) is a private defense contractor, known for the production of UAVs and radio frequency (RF) equipment for the Russian armed forces, as well as for other government customers.
According to the Lookout researchers, the STC Monokle surveillance malware and Android protection package called Defender is digitally signed with the same cryptographic certificates and also has the same command and control infrastructure.
“The command and control infrastructure that interacts with the Defender application also interacts with the Monokle surveillance malware samples. The signature certificates used to sign Android application packages also overlap between Defender and Monokle surveillance malware, “the report states.
“Lookout researchers observed a further overlap between Monokle surveillance malware and the security software created by STC in the choice of authors during design and implementation.”
Monokle surveillance malware for iOS in development
In addition to Android, the researchers also found some Monokle malware samples, an analysis of which revealed the existence of Monokle surveillance malware versions for iOS designed for Apple devices, although at the time the researchers did not find evidence of active infection from iOS.
Also Read: Hackers Can Change Media Files We Recieve Via Whatsapp Or Telegram Using Media File Jacking
Some teams in the malware examples seem to be useless as part of the Android client and have probably been added unintentionally, suggesting that versions of iOS Monokle are under development.
These commands include iOS keychain features, iCloud connections, Apple iWatch accelerometer data, iOS permissions, and other iOS services or services.
According to the Lookout researchers, Monokle surveillance malware is used to target attacks against a limited number of people in the Caucasian regions of Eastern Europe, as well as those interested in Islam and the Ahrar al-Sham militant group in Syria and the people in the Central Asian country. and the former Soviet Republic of Uzbekistan.



