In case you receive an photo document sent by way of a person, even your pal, to your fb Messenger, LinkedIn or any other social media platform, just DO not ON IT.
Even JPG photograph file ought to in the end infect your pc with the notorious Locky Ransomware.
Earlier this week, we mentioned a brand new assault marketing campaign that used fb Messenger to spread Locky Ransomware via .SVG image documents, despite the fact that facebook denied this turned into the case.
Now, researchers have located that the continuing spam marketing campaign is likewise the use of boobytrapped .JPG photograph files so that you can down load and infect customers with the Locky Ransomware via facebook, LinkedIn, and different social networking systems.
Safety researchers from Israeli safety firm take a look at factor have reportedly determined how cyber criminals are hiding malware in picture documents, and the way they may be executing the malware code within those pix to infect social media users with Locky versions.
Consistent with researchers, malware authors have found security vulnerabilities within the facebook and LinkedIn that forcibly down load a maliciously coded image file on a person’s laptop, even though in some cases, the user has to click on at the image report to download.
While the consumer detect the automatic download and get right of entry to that malformed picture record, malicious code installs the Locky ransomware onto the consumer’s pc, which encrypts all documents on the infected pc until a ransom is paid.
Flaws in facebook and LinkedIn stay Unpatched
the safety firm has declined to offer technical info because the vulnerability the malware relies on still influences both facebook and LinkedIn, among other unnamed net offerings.
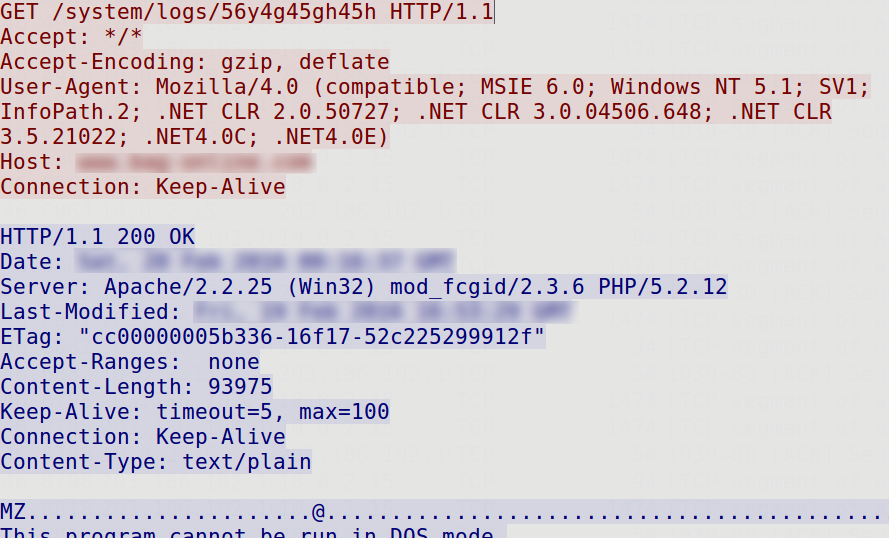
“The attackers have constructed a new capability to embed malicious code into an photograph document and effectively upload it to the social media internet site,” check factor researchers say.
“The attackers take advantage of a misconfiguration at the social media infrastructure to intentionally force their sufferers to download the photo document. This results in infection of the customers’ device as soon as the quit-consumer clicks at the downloaded record.”
CheckPoint says the company said the problem to each facebook and LinkedIn back in September, but the vulnerabilities continue to be unpatched in both the platform, which is now actively being exploited by way of attackers.
Video Demonstration of the assault
you can also watch the video demonstration of this assault, which CheckPoint dubbed ImageGate, which shows the assault in motion.
Locky is Spreading vastly via Social Media Platform

Locky ransomware has been round when you consider that early this yr and has come to be the most important and most common ransomware own family recognized nowadays. it works by way of encrypting sufferers’ files with RSA-2048 and AES-1024 algorithms and needs a ransom for the important thing.
Locky ransomware especially spreads thru phishing emails containing a malicious attachment disguised as a word or Zip record. but in view that human beings spend time on social community sites, cyber crooks have grew to become their recognition to finding a manner into those structures.
take a look at point says that in the beyond week, they have noticed a “large unfold of the Locky ransomware thru social media, mainly in its fb-based campaign.”
To hold yourself safe, you are cautioned now not to open any unsolicited file that has robotically downloaded onto your computer, mainly picture documents with uncommon extensions like SVG, JS, or HTA.
the bottom line: do not be curious to study photo sent by a person, as a minimum in the mean time.



