“Linux doesn’t get viruses” — it’s a fantasy.
A brand new Trojan has been discovered within the wild that turns Linux-primarily based gadgets into proxy servers, which attackers use to defend their identity at the same time as launching cyber attacks from the hijacked systems.
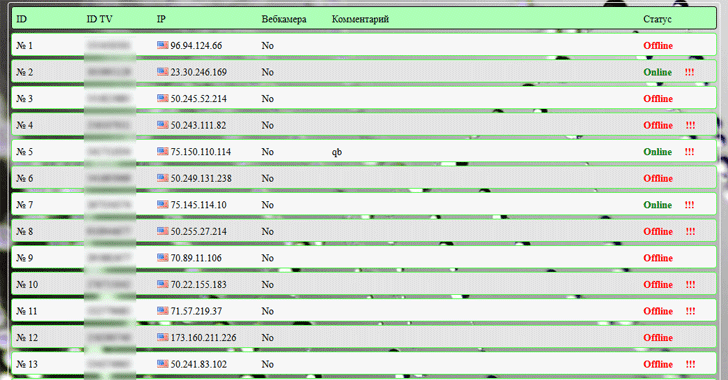
Dubbed Linux.Proxy.10, the Trojan became first noticed at the stop of final 12 months via the researchers from Russian security firm medical doctor net, who later identified thousand of compromised machines via the quit of January this 12 months and the marketing campaign remains ongoing and hunting for greater Linux machines.
Consistent with researchers, the malware itself doesn’t include any exploitation module to hack into Linux machines; as a substitute, the attackers are the usage of other Trojans and techniques to compromise devices at the primary place and then create a new backdoor login account the usage of the username as “mother” and password as “fucker.”
As soon as backdoored and the attacker receives the listing of all efficaciously compromised Linux machines, after which logs into them through SSH protocol and installs the SOCKS5 proxy server the use of Linux.Proxy.10 malware on it.
This Linux malware isn’t at all state-of-the-art since it makes use of a freeware supply code of the Satanic Socks Server to setup a proxy.
Consistent with the security firm, heaps of Linux-primarily based gadgets have already been infected with this new Trojan.
except this, the same server — belonging to the cyber criminals who distribute the Linux.Proxy.10 malware — now not simplest contained the list of compromised gadgets but also hosted the manage panel of a spy-Agent laptop tracking software program and a windows malware from a recognized family of Trojan spyware, referred to as BackDoor.TeamViewer.
This isn’t always the primary time when such Linux malware has been discovered.
Over a yr in the past, ESET security researchers uncovered a similar malware, dubbed Moose, that also had the capability to show Linux devices into proxy servers that have been then used for launching armies of fake money owed on social media networks, including Instagram, and Twitter.
Linux customers and administrators are advocated to tighten SSH protection by way of limiting or disabling far off root access through SSH, and to know in case your machine has already been compromised, keep a ordinary watch on newly generated login users.



