Are you sure that the version of WhatsApp or Skype or VLC Player installed on your device is legitimate?
Security researchers have discovered that the legitimate download of several popular applications such as WhatsApp, Skype, VLC Player and WinRAR have been compromised at the ISP level to distribute known spyware also known as FinFisher FinSpy.
FinSpy is a highly secret surveillance tool that was previously associated with the British company Gamma Group, a company that legally sells surveillance and spying programs to government agencies around the world.
Spyware has extensive intelligence capabilities on an infected computer, including managing live secret surveillance, activating webcams and microphones, recording every victim with a keylogger, which intercepts Skype calls and file exfiltration.
Also Read: Unofficial Anonymous Hacker Guide For Security Enthusiasts
To get into the target machine, FinFisher spyware typically uses various types of attacks, including phishing for the spear, manual installation with physical access to the device, zero-day attacks, and attacks for irrigation.
Your ISP can help hackers spy on you
However, a new report released today by ESET said its researchers have uncovered new surveillance campaigns with new variants of FinFisher spyware in seven countries, which comes in a legitimate application.
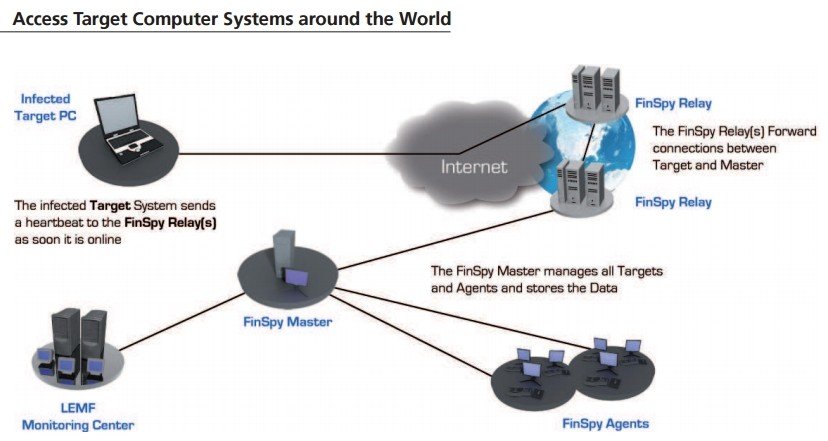
But how is it happening? Attackers are focusing on victims with a man in the middle of the attack (MitM), where Internet service providers (ISPs) are most likely working as a “broker” -bundling legitimate FinFisher spyware software download.
“We saw that this vector is used in two of the countries where systems have ESET detected the latest FinFisher spyware (in the five remaining countries, the campaigns were based on the traditional media of infection),” say researchers.
Also Read: Steps You Should Take To Protect Yourself From Equifax Data Breach
Previously published documents by WikiLeaks have also indicated that the manufacturer FinFisher spyware also offered a tool called “FinFly ISP”, which must be distributed at the ISP level with the functionality required to carry out an attack of this type MitM.
In addition, the technique of infection (using HTTP 307) redirection is implemented in the same way in the two affected countries that ESET discovered to be the target of new variants of FinFisher spyware. However, the company did not name the affected countries as “not putting anyone in danger”.
Another fact supporting the MitM attack at the ISP level is that all relevant objectives identified by researchers within a country were using the same ISP.
“Finally, we used the same redirection method and format for Internet content filtering by ISPs in at least one of the affected countries,” says the ESET report.
Also Read: How To Organize Your Office Like A Boss
Directed popular applications of new variants of FinFisher spyware include WhatsApp, Skype, VLC Player, Avast and WinRAR and ESET researchers stated that “virtually any application could be misused.”
Here’s how the attack works:
When end users demand one of the affected applications from legitimate sites and click on the appropriate download link, you will see a modified URL, which redirects the victims to a Trojanized installation package hosted on the attacker’s server.
This involves installing a version of the legitimate application provided with the monitoring tool.
“Redirection is achieved by the legitimate download link replaced by a malicious one,” say the researchers. “The malicious link is sent to your browser by an HTTP 307 temporary status redirect response code indicating that the requested content has been temporarily moved to a new URL.”
Also Read: Dragonfly Hacking Group Infiltrated the US And European Power Plants
This redirection process, according to the researchers, is “invisible to the eye” and occurs without the knowledge of the user.
FinFisher Spyware that uses many new tricks
The new tricks used by the latest version of FinFisher spyware prevented it from being discovered by the researchers.
The researchers also note that the latest version of FinFisher spyware received several technical improvements in stealth, including the use of custom virtualization codes to protect most of its components, such as the core controller.
It also uses anti-disassembly and numerous anti-enclosure, anti-debugging, anti-virtualization and anti-emulation tricks, designed to compromise end-to-end encryption software tricks and known privacy tools.
Also Read: Project Protego CIA’s Secret Missile Control System Unveiled By Wikileaks
One of these secure messaging applications, called Threema, was discovered by researchers while they were analyzing the latest campaigns.
“FinFisher spyware software is disguised as an executable file called” Threema. “Such a file could be used to target users interested in privacy since Threema’s legitimate application provides secure instant messaging with end-to-end encryption.”
“Ironically, being tricked into downloading and executing the infected file may lead to an exploration of a user’s privacy intent.”
Gamma Group has not yet responded to the ESET report.



