Phish creators have recently come across an extension for Google chrome extension to push malware after compromising the Chrome Web Store account of German software developers a9t9 and abused to distribute spam messages to users who are not accusing.
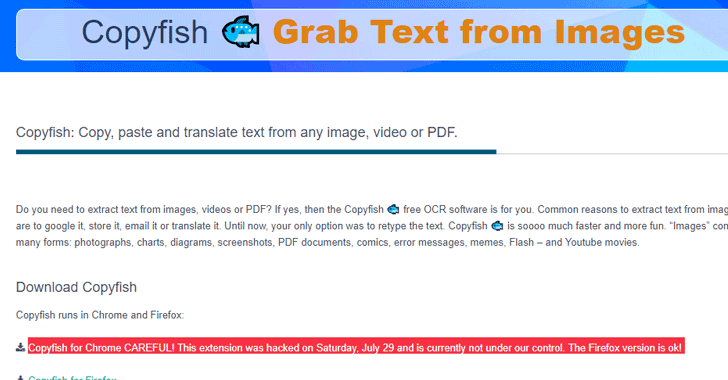
Nicknamed Copyfish, Chrome Extension To Push Malware which allows users to extract text from images, PDF, and video documents and has more than 37,500 users.
Unfortunately, the Copyfish Chrome Extension To Push Malware was deceived and compromised by unknown attackers, which comes with expanding advertising injection capability. However, Firefox’s counterpart was not affected by the attack.
The attackers have also moved the extension of their account for the prevention development of the developers to delete the file from the infected file even after it has been identified that the extension has been compromised.
Also Read: Apple Remove VPN Apps From China App Store
“So far, the update looks like a standard adware cut, but so far we have no control over Copyfish, thieves could upgrade the extension again … until we receive it,” warned the developers. “We can not even turn it off since it’s no longer in our developer account.”
This is how hackers have gained the Chrome Extension To Push Malware:
Copyfish developers have tracked down the trick for a phishing attack that took place on July 28.
According to an a9t9 software, one of the members of their team received a phishing e-mail posing as the Chrome Web Store team that told them to update Chrome extension Copyfish; Otherwise, Google will remove it from the web store.
The phishing email instructed the member to click “Click here to read more details”, which opened the “Google” dialog box.
The link was a bit.ly link, but because the team member was showing the link in HTML format, he did not find it immediately suspicious and typed the password for his developer account.
Developers have said that the password was almost exactly the one used by the Google display. Even though the computer does not have a fake password screen page, since it only appeared once, it did a screenshot of the email spoofing and its initial response.
“This seemed legitimate to the team member, so we did not notice the [phishing] attack like this at this point. [Phishing] for Chrome Extension To Push Malware simply was not on our radar,” he told the developers.
Once the developer has entered the credentials of the a9t9 software developer account, the hackers behind the attack have updated the Copyfish extension July 29 to version 2.8.5, which is pushing spam and ads to users.
The worst is when those responsible for Copyfish noticed the problem very quickly but could not do anything because the hackers have changed the extent of their account for development.
Also Read: Google Detected Dangerous Lipizzan Spyware Apps On Play Store
The software company has contacted Google developer support, which is currently working to provide the company with access to its software.
The a9t9 software warns users that the Copyfish Chrome extension is not under their control. Therefore, users are advised not to install the malicious Chrome extension and remove them if they have already been installed.



