Every other horrific information for Android customers — supply code for another Android banking malware has been leaked online thru an underground hacking discussion board.
This newly located banking Trojan is designed to steal cash from bank money owed of Android gadgets’ proprietors by means of gaining administrator privileges on their smartphones.
Seemingly, it will appeal to the eye of many cyber criminals who can recompile the supply code or can also use it to expand more custom designed and advanced versions of Android banking Trojans.
In keeping with security researchers from Russian antivirus maker Dr. internet, the malware’s source code turned into published online, together with the facts on the way to use it, that means Android devices are most in all likelihood to receive more and more cyber assaults in upcoming days.
Leaked: Trojan source Code + ‘a way to Use’ commands
Dr. internet researchers stated they have got already determined one banking trojan within the wild evolved the usage of this leaked source code, adding that the Trojan is distributed as popular apps both directly injected in APKs available on-line or in third-celebration app shops.
Dubbed BankBot, the trojan has the ability to get administrator privileges on inflamed gadgets. once it receives complete privileges, the malware trojan gets rid of the app’s icon from the smartphone’s home display screen with a view to trick victims into believing it turned into removed.
But, the BankBot trojan remains energetic inside the historical past, expecting commands from attacker’s command and manipulate (C&C) server. It observed targeting best users of Russian banks.
BankBot has the capability to carry out a wide range of responsibilities, such as send and intercept SMS messages, make calls, music devices, thieve contacts, display phishing dialogs, and scouse borrow sensitive information, like banking and credit card info.
“Like many different Android bankers, [BankBot] steals private person information with the aid of monitoring the release of online banking apps and fee system software program. One pattern examined by using doctor web’s safety researchers controls over three dozen such applications,” the researchers explains.
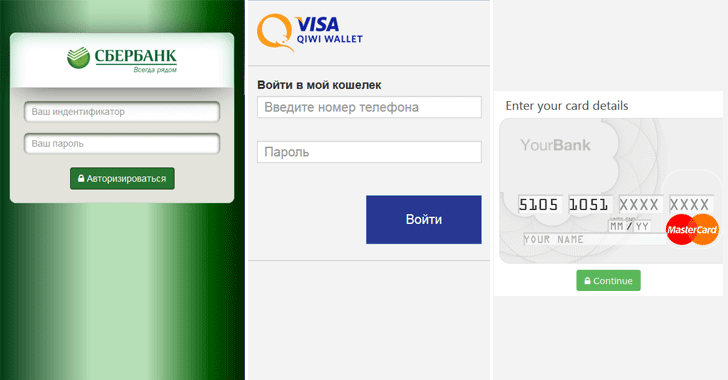
“Once Android.BankBot.149.starting place detects that any of the aforementioned packages were launched, it loads the applicable phishing input form to get right of entry to person financial institution account login and password records and presentations it on pinnacle of the attacked application.”
Why ought to You worry approximately BankBot?
The malware hides itself until the sufferer opens any mobile banking or social media app. as soon as the victim opens one such app, BankBot launches a phishing login overlays, tricking sufferers to re-authenticate or re-enter their payment card information.
The gathered facts is then despatched back to on-line servers, in which the attackers can get entry to the stolen information.
BankBot can phish credentials for apps such as facebook, WhatsApp, Instagram, Twitter, Youtube, Snapchat, Viber, WeChat, imo, Uber, and the Google Play store.
except this, the BankBot trojan also can intercept textual content messages, ship them to the attackers, and then delete them from the victim’s telephone, which means that bank notifications by no means attain the users.
How to shield your self towards such attacks?
Now, this is simply one piece of malware evolved the usage of the publicly available supply code and observed via researchers. There are possibilities that greater such malware are available focused on Android gadgets but now not yet caught.
To prevent yourself in opposition to such attacks, as I formerly endorsed, you’re counseled to:
- Usually be first rate-careful when downloading APKs from third-party app stores. visit Settings → security and then flip OFF “allow set up of apps from resources apart from the Play save.”
- Never open attachments from unknown or suspicious resources.
in no way click on on hyperlinks in SMS or MMS sent for your cellular telephone. - Although the e-mail appears legit, cross without delay to the internet site of origin and
- Verify any feasible updates.
- Usually hold your Anti-virus app updated.
- Hold your wireless grew to become OFF while now not in use and avoid unknown and unsecured wireless hotspots.



